How can I be hacked?
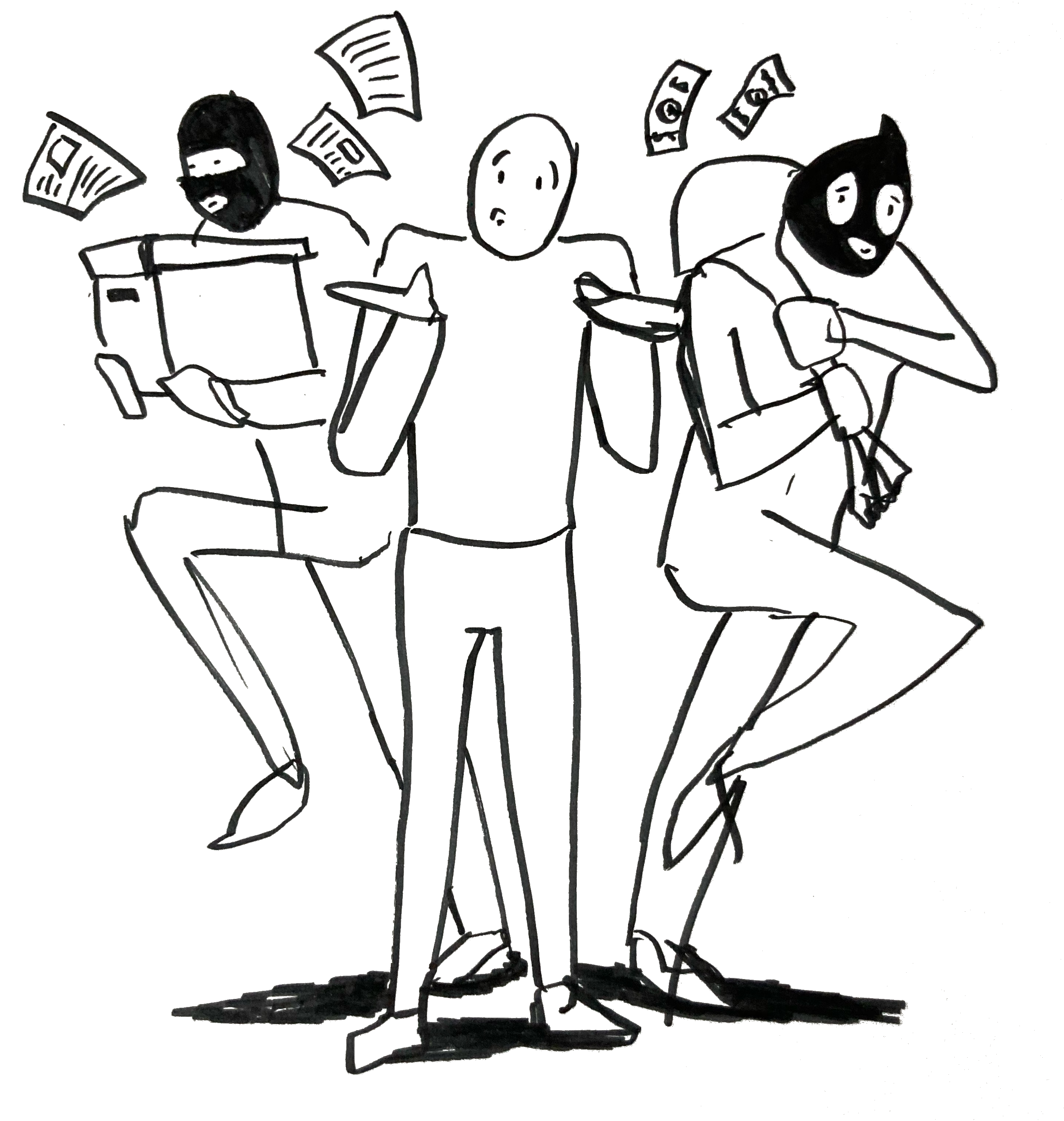
Yes, there are hackers who want to steal your cash. In the last section, it became clear that hackers target anyone who can make them money.
But what will a cyber-criminal actually do to compromise your security?
Unfortunately, the quick answer is, “we don’t really know.”
There is plenty of cybersecurity research out there, and there are plenty of ways to stay safe, but there is no good overall list of consumer cybersecurity threats. Without a well-tested list, we have no way to rank the most likely threats.
Instead, the best we can do is analyze the threats we know about—and hope we didn’t miss any.
Our best list: the VERIS schema
The best starting point we have comes from the VERIS schema(Actions, n.d.), developed at Verizon for their annual Data Breach Investigations Report, mentioned in the last section.
The VERIS schema breaks up attacks into 7 different categories, called “actions.” Each of these is actually pretty understandable:
- Hacking: things like using stolen passwords, exploiting vulnerabilities, and everything you’ve seen on NCIS.
- Malware: things like computer viruses.
- Social: phishing and other attacks involving manipulation.
- Misuse: things like admins abusing access to emails and logs.
- Physical: things like stealing a laptop.
- Error: things like emailing the wrong person or accidentally leaking information.
- Environmental: things like storms, pathogens, power outages.
For corporate threats, at least, this is a fantastic, battle-tested list. The DBIR analyzes over 40,000 security incidents annually, and 94% of attacks fall into one of these categories(Verizon Enterprise, 2018, p. 22).
If this list were tested on consumers, rather than just corporations, it would be exactly what we’re looking for.
The best list is not good enough
Unfortunately, no one has applied this list to consumers, or even tested the list on them.
Beyond that, it’s pretty easy to identify some problems applying this list to everyday folks:
- The list masks a big problem—that hackers are far more likely to get your password by hacking a corporation, rather than hacking you.
- This list categorizes a lot of problems (like accidentally making a Facebook album public) as “error,” which masks their true cause: lots of software makes it hard to stay safe(Norman, 2002, p. viii).
- Almost no research analyzes the consumer impact of the last 4 actions in the list (misuse, physical, error, and environmental).
The VERIS attack types simply aren’t a complete answer here. Until someone takes a systematic look at the problems everyday users face, we won’t have that complete answer.
You don’t need a complete list to be smart
But you don’t need a complete list to start making smart decisions. You just start with the data you have.
Consider your friend who never buckles up when they drive (we all have one). “It’s not safe!” you say.
“Ah,” they reply, with an infuriating grin, “but I’ve never had an accident.”
Perhaps they’re right: after all, they haven’t been hurt yet, and plenty of folks get hurt in car accidents even while wearing their seatbelts. By a similar argument, why don’t you wear a bulletproof vest when you walk to work? Doesn’t it make you “safer”?
For me, the answer is immediate and visceral. Getting shot is not likely. Getting in a car accident is. We have the data for that. Seatbelts and bulletproof vests make you “safer” in different scenarios. If my friend wore the vest but not a seatbelt, I’d want to slap them.
But in some places, those likelihoods are flipped (like a war zone). And in those cases, I’d rather wear the vest than buckle up.
No list can ever be complete
It’s worth noting that no list of threats can ever be complete. This comes from a deeper philosophical issue, the problem of induction(Herley & van Oorschot, 2018, p. 2; Herley, 2016, p. 2), but think about it: each list comes with its own assumptions—of what’s important to you, of what an “attack” means, of what’s possible. Even if we analyzed every bit of data we have, we’d still be limited by the attacks we know about or can imagine.
Without even a battle-tested overview of threats, no matter how much energy you spend protecting yourself, you can never be sure that you protected against the most important threats. You might be wearing a seatbelt when you should be wearing a bulletproof vest.
Ranking threats in the absence of data
In the absence of data, remember the takeaway from the last section: unless they are targeting you specifically (in which case you should get help), hackers need money.
You can use that knowledge to roughly rank the attacks you know about, like those in the VERIS schema (even with its caveats). You might not know precisely how these attacks work or what these attacks mean specifically, but you should have an intuition for what can pay a hacker’s rent and what can’t.
Ask yourself: how many passwords could a hacker get by sniffing the wi-fi at Starbucks? Or by physically watching over people’s shoulders there?
And how many more passwords could they get if they used that time to send phishing emails instead?
You can also combine that idea with other stuff you know—for example, multiple Microsoft reports note that accounts with 2-factor authentication are more than 99.9% safer(Goyal, 2019; Weinert, 2019; Weinert, 2019) than accounts with just a password (see Passwords & TFA). But you might have been able to guess that anyway (is it easier for a hacker to impersonate your phone number or to guess your password, password1?).
This is the key: you are already well-equipped to understand how easy or difficult many of these attacks are. More knowledge can only help, but you should already be ready to start.
Conclusion
Still, you should be unhappy with these answers.
Real answers would give you numbers and put things in perspective. They would point out all of the important things, and they would feel complete. They’d help you feel like a doctor, looking at efficacy and rates of side effects to choose the right treatment plan. They would let you rank threats, and they’d help you focus on the biggest ones.
We don’t have those answers.
Corporations do: they have the VERIS schema attack types. The DBIR gives them tips, like “malware is much more common than physical attacks.” But these attack types aren’t a perfect fit for everyday folks.
So make do.
- Use your knowledge of what hackers want to rank threats.
- Use the VERIS schema attack types to (at least) get a sense of what’s possible.
- Realize that there might be more important threats & defenses just out of sight, ready to be discovered.
And demand a better answer to the question: “how will I be hacked?”